Queen Triggerfish Vector. Colorful Exotic Tropical Fish Isolated on White Background. Ocean Animal, Funny Sea Life Cartoon Stock Vector - Illustration of ocean, balistes: 56323605
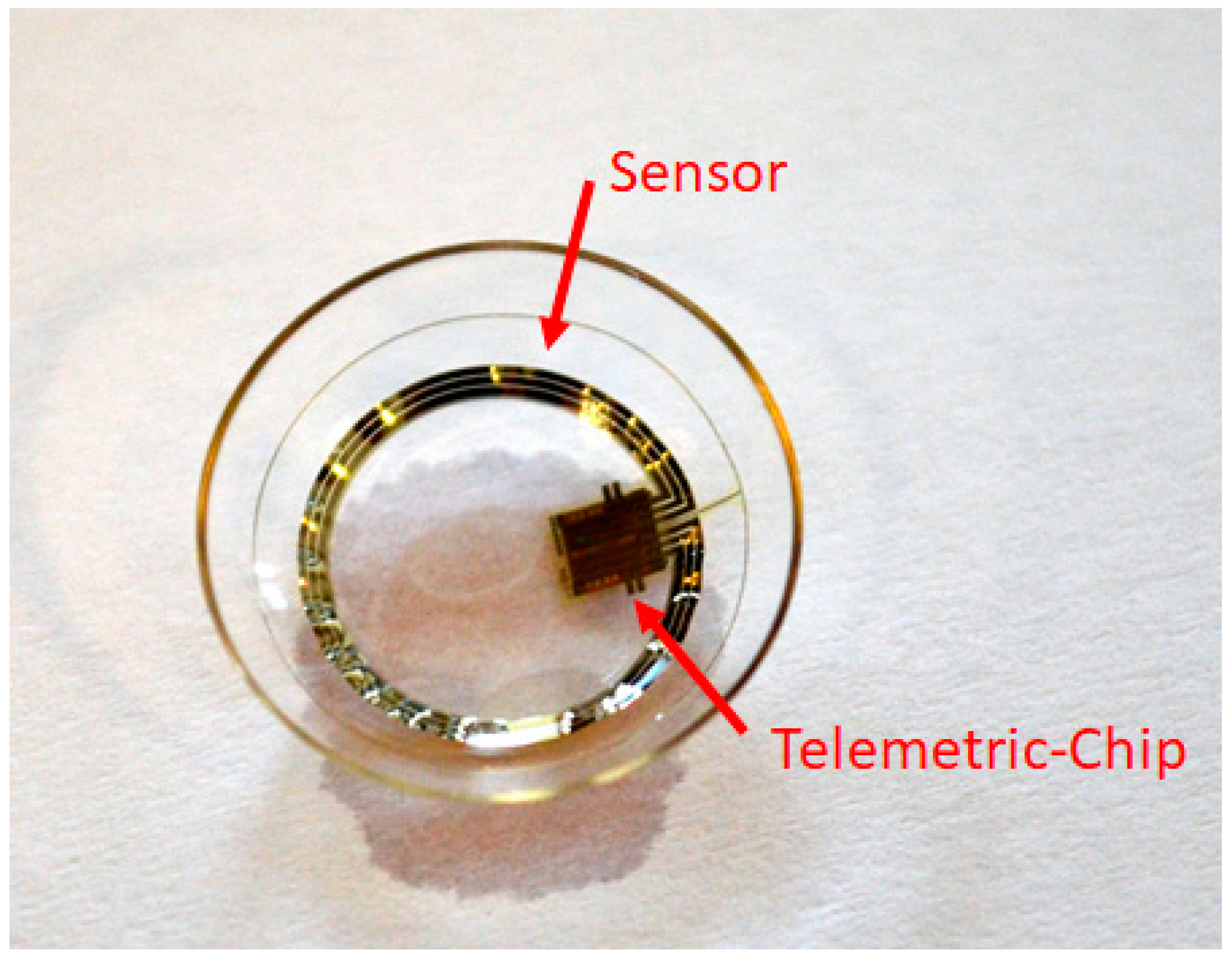
JCM | Free Full-Text | Triggerfish Recording of IOP Patterns in Combined HFDS Minimally Invasive Glaucoma and Cataract Surgery: A Prospective Study

As Santa Clara County procures 'stingray' cell tracker, increased scrutiny surrounds potentially invasive device – The Mercury News
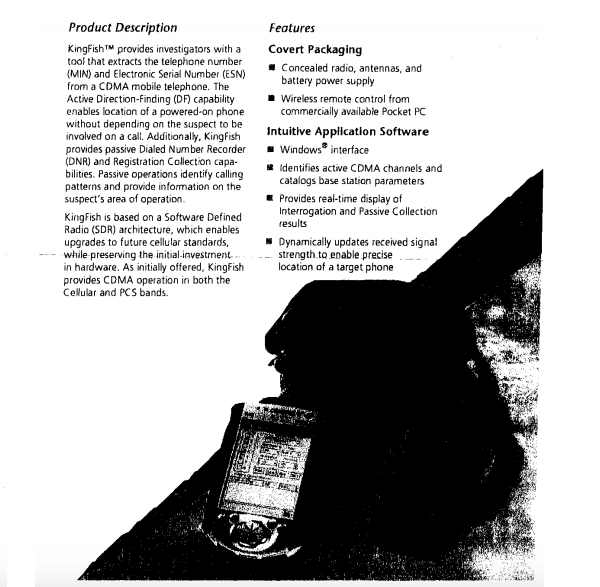
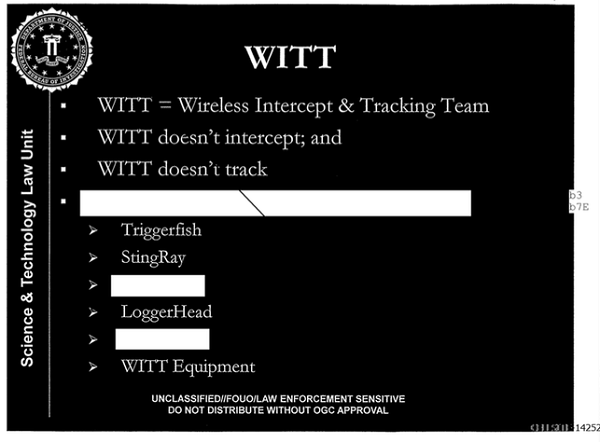
The Forensic Science of IMSI/TMSI catchers: Stingray, Gossamer, FishHawk, Porpoise, and others | The Truth About Forensic Science

Hot Style Cell Phone PC Hard Case Cover // M00129878 Fish Triggerfish Hidden Crevice Reef // BlackBerry Q10 : Amazon.co.uk: Electronics & Photo